Admin Capabilities
Understand administrator roles, permissions, and what each page allows.
Last updated: 2026-01-29 Where to find it: Roles, Permissions, Tenants, Feature Flags (left sidebar) Who can use it: Platform admins; some sections require elevated permissions Prerequisites: Admin role with the required capabilities Help link: /admin-guide
How to do it
Check your permissions
- Click your avatar → My Profile.
- Review the Roles section to see assigned roles and permissions.
Create a custom role
- Go to Roles → Create Role.
- Enter a Name and Description.
- Select the Permissions the role should include.
- Click Create.
Enable a feature flag
- Go to Feature Flags.
- Find the flag to enable.
- Toggle it on.
- Select the scope (platform, tenant, or user).
What you'll see (fields/columns)
Administrator types
Platform administrators manage the entire DigiWedge platform and can access all organizations.
| Role | Description |
|---|---|
| Admin | Full access to all platform features |
| Manager | Manage organizations and users |
| Auditor | Read-only access for compliance review |
Tenant administrators manage a single organization only.
| Role | Description |
|---|---|
| Owner | Full access within the organization |
| Admin | Manage users, roles, and settings |
| Editor | Limited management capabilities |
Tenants
| Field | Type | Description |
|---|---|---|
| Name | Text | Organization name |
| Slug | Text | URL-friendly identifier |
| Status | Badge | Active or Inactive |
| Created | Timestamp | When the organization was created |
SCIM provisioning
Use SCIM to keep your tenant’s user directory in sync with your identity provider.
How to configure
- Go to Tenants and select SCIM for the tenant.
- Toggle Enable SCIM to activate provisioning.
- Copy the SCIM base URL and generate an access token.
- Paste the URL and token into your IdP’s SCIM configuration.
Token rotation
- Use Rotate Token whenever you suspect exposure or on a scheduled cadence.
- The token is shown once; store it securely in your IdP vault.
- Revoke Token immediately disables SCIM authentication for the tenant.
SCIM base URL format
https://idp.<env>.digiwedge.com/api/scim/v2/tenants/<tenantId>
SAML SSO
Use SAML to enable single sign-on for a tenant.
How to configure
- Go to Tenants and select SAML for the tenant.
- Upload your IdP metadata XML or paste the metadata URL.
- Confirm the ACS URL and Entity ID values.
- Save the configuration and run a test login from your IdP.
Troubleshooting
- Ensure the tenant is active and SAML is enabled.
- Re-check the IdP metadata and clock skew settings if assertions are rejected.
Roles
| Field | Type | Description |
|---|---|---|
| Name | Text | Role display name |
| Description | Text | What this role is for |
| Permissions | Tags | Assigned permissions |
| Users | Numeric | Number of users with this role |
Permissions
| Field | Type | Description |
|---|---|---|
| Feature | Text | The feature this permission belongs to |
| Action | Text | The action (read, create, update, delete) |
| Description | Text | What this permission allows |
Permission assignments
| Field | Type | Description |
|---|---|---|
| Role | Text | The role receiving the permission |
| Permission | Text | The permission being assigned |
| Scope | Badge | Platform-wide or tenant-specific |
Features
| Feature | Description |
|---|---|
| User Management | Adding, editing, and removing users |
| Role Management | Creating and configuring roles |
| Tenant Management | Managing organizations (platform only) |
| Permission Management | Defining permissions (platform only) |
| Invitation Management | Sending and managing invitations |
| Session Management | Viewing and revoking sessions |
| Feature Flags | Toggling feature availability (platform only) |
Feature flags
| Field | Type | Description |
|---|---|---|
| Name | Text | Flag identifier |
| Description | Text | What this flag controls |
| Status | Toggle | Enabled or Disabled |
| Scope | Select | Platform, Tenant, or User level |
Consents
| Field | Type | Description |
|---|---|---|
| Name | Text | Consent identifier |
| Description | Text | What users are agreeing to |
| Required | Toggle | Whether consent is mandatory |
| Version | Text | Current consent version |
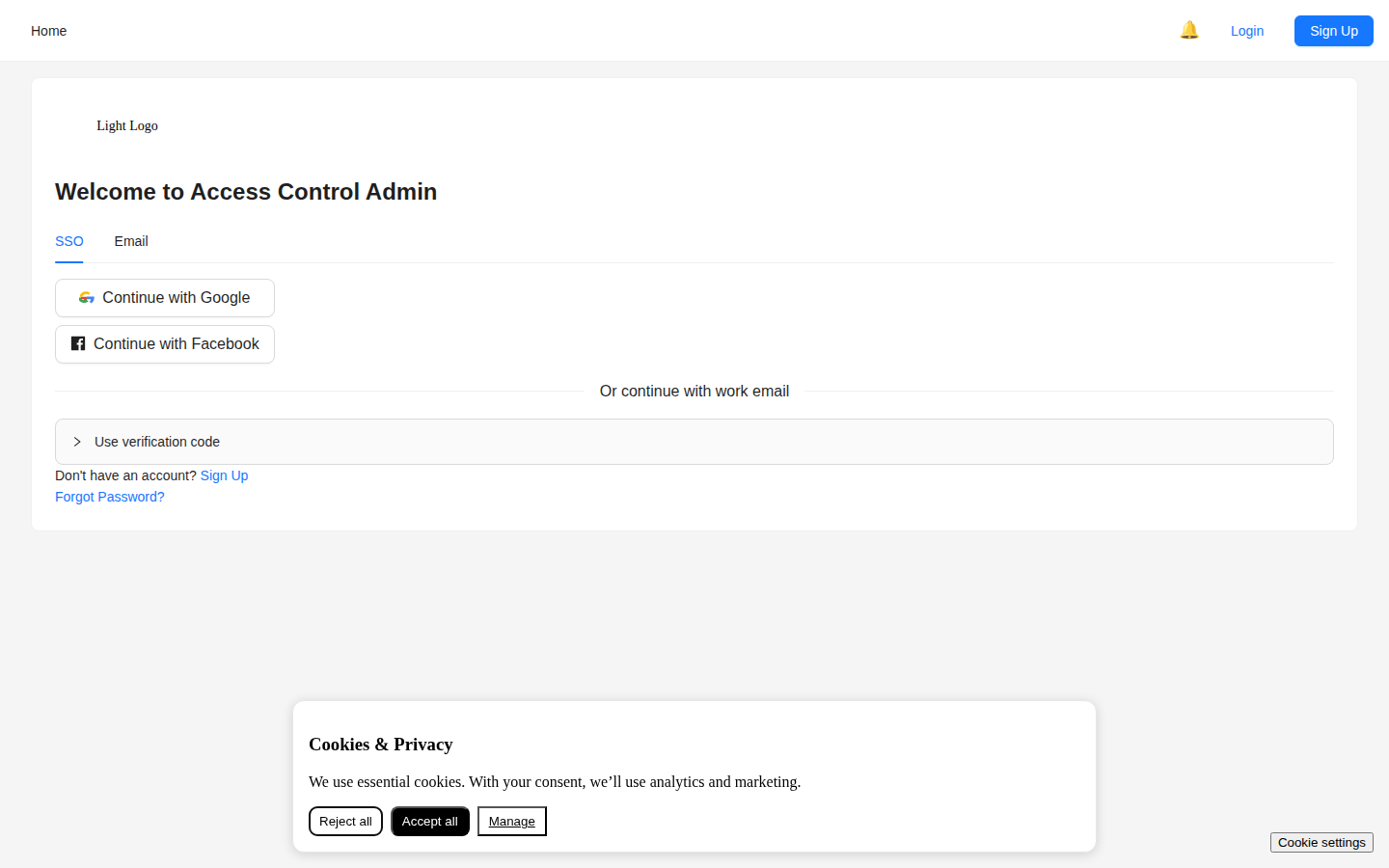
Screenshot / Callout
Expected outcome
- Roles and permissions reflect the access model your organization requires.
- Tenants and platform features are visible only to authorized administrators.
Troubleshooting
- Can't see a menu item? Your role doesn't have the required permission.
- Can't create users? You need the User Management: Create permission.
- Feature flag not working? Check the scope; it may only apply to specific tenants.
- Role changes not taking effect? Users may need to sign out and back in.
Related
- User Management — Managing users
- Onboarding Wizard — Setting up new organizations
- Glossary — Permission and role terminology